GRC is the White Team of cybersecurity, I call us “The Peaceful Angels” We’ve heard people say GRC is the non-technical aspect of cybersecurity, this is not 100% true, sorry to disappoint you. There are some technical aspect to GRC that makes you stand out from the “regular” GRC professional such as the use of Data Analytics tools, Active Directory, performing some duties of both the Red and Blue team to detect vulnerabilities and threats… so much more to make you stand out from others in this field.
Most importantly when it comes to standing out, it is necessary but not IMPORTANT to learn a programming language as a cybersecurity expert.
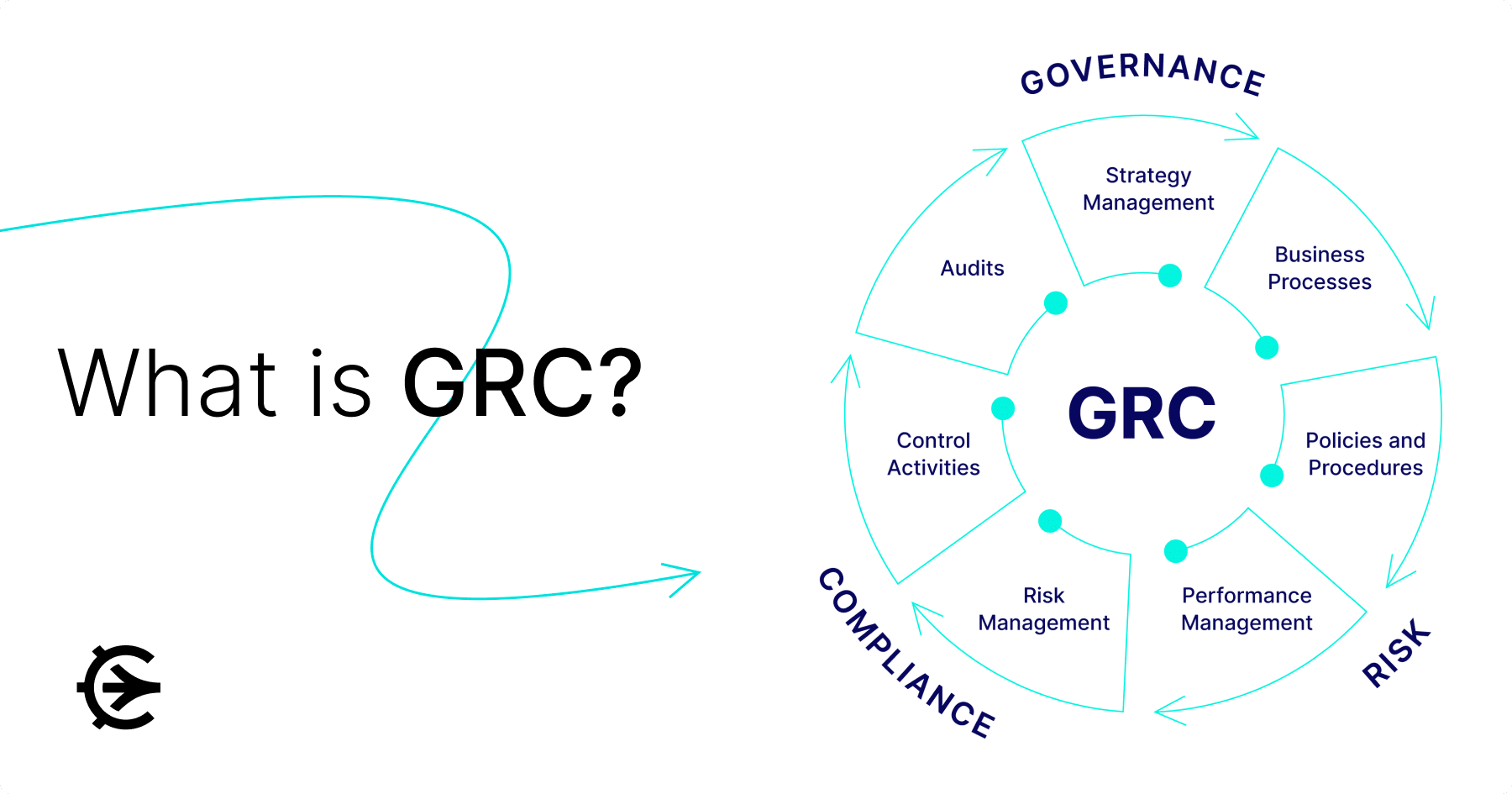
G- Governance. This stands for the general rule that facilitates the implementation of Risk, Policies, Compliance and Frameworks… Governance provides that shield for investors, clients or business partner to have confidence about a business and it contributes significantly to the overall GRC strategy and implementation.
R- Risk. What is Risk?? If you can define risk in your own term then, Risk in GRC is the process of identifying, mitigating, and assessing potential threats and vulnerability within an organization. Identifying threat/vulnerability sounds like something a pen tester/ ethical hacker should involve in yea? As a risk professional, its your duty to identify and mitigate against risks in your organization because exposure to risk may cost you a lot more than ignoring it.
C- Compliance. Comply!!! Adhere to!!! Compliance in GRC means adhering to set rules and regulation governing tools, data, information you have access to. For data we have GDPR which helps regulate the use and processing of individual data. PCI DSS for card transactions, HIPAA for health record governance, SOX for finance, ISO 27001 for Information security… and many more. If your company doesn’t comply to these bodies related to what industry they are, they get fined a huge amount of money. As a compliance officer, its your duty to be sure your organization complies to the policies and set rules.
Basics
Introduction To Cybersecurity by Cisco or any platform that works for you.
> Cybersecurity Essentials by CompTIA (not sure its still there but studying ISC2 will help
> GRC crash course on Udemy
Intermediate Certifications
> CompTIA Security+
> CGRC
Advanced Certification (some can only be written if you have 5 years experience above)
> CISA
> CISM
> CRISC
> CISSP
Some Roles in GRC
GRC Analyst
IT Auditor
Compliance Officer
Policy Writer
Risk Manager
Compliance Analyst
Risk Analyst etc
Transitioning from other career? you’ll have a soft landing in GRC. If you are a lawyer you can work for law firms as data privacy officer, from a science/health related field you can dive into working for health firms understanding HIPAA, from banking, your knowledge of KYC/AML will help you a lot, as a Data Analyst, all your skills matter in this path. There are a lot of opportunities in GRC that can be explored just ensure you have passion for what you’re doing.
Interesting about this field is that you can apply to different roles even after picking a career path, just be sure to know how to perform on that role, tweak your CV towards that role and apply. With or without certification, you can succeed in this path.
Welcome to GRC!!!!

A WordPress Commenter
April 2, 2026 at 10:05 amHi, this is a comment.
To get started with moderating, editing, and deleting comments, please visit the Comments screen in the dashboard.
Commenter avatars come from Gravatar.